Showing all posts by Noam Dotan

How to Mitigate the Risk of GitHub Actions
How to Mitigate the Risk of GitHub Actions. Get highlights of our research into the security of GitHub Actions, and our advice on mitigating the risk.
Read More
Preview of State of GitHub Actions Security Report: Security of GH Workflows Building Blocks
Security of the Building Blocks of GitHub Actions Workflows. Understand the security status of GitHub Actions workflows and how to mitigate the risk.
Read More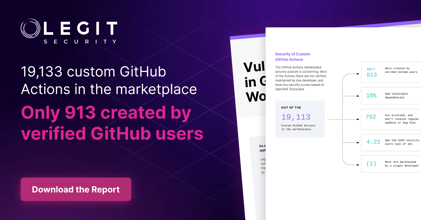
Security of Custom GitHub Actions
Security of Custom GitHub Actions. Get details on Legit's research on the security of custom GitHub Actions.
Read More
Announcing The State of GitHub Actions Security Report
Announcing the State of GitHub Actions Security Report. Get details on Legit's research on the security of GitHub Actions.
Read More
Using AI to Reduce False Positives in Secrets Scanners
Using AI to Reduce False Positives in Secrets Scanners. Get an overview of how secrets scanners work, and how Legit is reducing secret-scanning false positives..
Read More





GitHub Codespaces Security Best Practices
GitHub configurations aren't secure out of the box. It's up to you to secure them. This blog discusses GitHub's new Codespaces product and how to secure it.
Read More

Google & Apache Found Vulnerable to GitHub Environment Injection
Learn how Legit Security discovered a vulnerable GitHub actions workflow that affected Google, Apache and potentially many more. Get details on the vulnerability and what you can do to mitigate it.
Read More
How Was LastPass Compromised?? Software Supply Chain Attack Tips
LastPass data breach: unauthorized access compromised developer accounts and proprietary source code. Learn about the LastPass security incident details and how to protect your business.
Read More
Vulnerable GitHub Actions Workflows Part 2: Actions That Open the Door to CI/CD Pipeline Attacks
We examine a bug we’ve found in a popular third-party GitHub action and how it could lead to your SDLC pipeline being attacked. Read more to improve GitHub security and secure your software supply chain.
Read More
Vulnerable GitHub Actions Workflows Part 1: Privilege Escalation Inside Your CI/CD Pipeline
Learn how Legit Security discovered a vulnerable GitHub actions workflow. Get details on the vulnerability and and what you can do to mitigate it.
Read MoreRequest a Demo
Request a demo including the option to analyze your own software supply chain.
